Safari for Mac
Configure Safari to Enable WebDriver Support. Safari’s WebDriver support for developers is turned off by default. How you enable it depends on your operating system. High Sierra and later: Run `safaridriver -enable` once. (If you’re upgrading from a previous macOS release, you may need to. Download Safari for Mac & read reviews. Apple’s browser tries to keep pace. Advertisement Platforms. Whether or not there is a better alternative to Safari for Mac is hard to answer. There are certainly faster browsers that. Only one Safari browser instance can be active at any given time, and only one WebDriver session at a time can be attached to the browser instance. These constraints ensure that the simulated behavior (mouse, keyboard, touch, and so forth) accurately reflects what a user can do in a macOS windowing environment and prevents tests from competing.
Safari is included with your Mac operating system.
Updating Safari

To keep Safari up to date for the version of macOS you're using, install the latest macOS updates.
The most recent version of macOS includes the most recent version of Safari. For some earlier versions of macOS, Safari might also be available separately from the Updates tab of the App Store.
Reinstalling Safari
If you deleted Safari and don't have a Time Machine backup or other backup, reinstall macOS to put Safari back in your Applications folder. Reinstalling macOS doesn't remove data from your computer.
Before reinstalling, you might want to use Spotlight to search for Safari on your Mac. If you find it, but it's no longer in your Dock, just drag it to the Dock to add it back.
Safari for Windows
Apple no longer offers Safari updates for Windows. Safari 5.1.7 for Windows was the last version made for Windows, and it is now outdated.
About Apple security updates
For our customers' protection, Apple doesn't disclose, discuss, or confirm security issues until an investigation has occurred and patches or releases are available. Recent releases are listed on the Apple security updates page.
Apple security documents reference vulnerabilities by CVE-ID when possible.
For more information about security, see the Apple Product Security page.
Safari 12.1
Released March 25, 2019
Safari Reader
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, and Mojave 10.14.4
Impact: Enabling the Safari Reader feature on a maliciously crafted webpage may lead to universal cross site scripting
Description: A logic issue was addressed with improved validation.
CVE-2019-6204: Ryan Pickren (ryanpickren.com)
CVE-2019-8505: Ryan Pickren (ryanpickren.com)
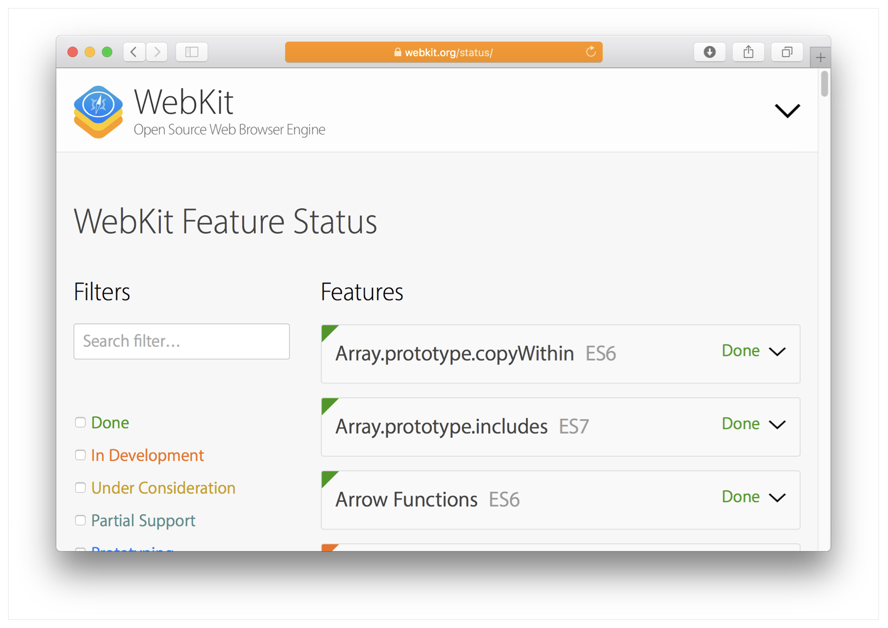
WebKit
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, and Mojave 10.14.4
Impact: Processing maliciously crafted web content may lead to arbitrary code execution
Description: A type confusion issue was addressed with improved memory handling.
CVE-2019-8506: Samuel Groß of Google Project Zero
WebKit
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, and Mojave 10.14.4
Impact: Processing maliciously crafted web content may lead to arbitrary code execution
Description: A memory corruption issue was addressed with improved state management.
CVE-2019-8535: Zhiyang Zeng (@Wester) of Tencent Blade Team
WebKit
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, and Mojave 10.14.4
Impact: Processing maliciously crafted web content may lead to arbitrary code execution
Description: Multiple memory corruption issues were addressed with improved memory handling.
CVE-2019-6201: dwfault working with ADLab of Venustech
CVE-2019-8518: Samuel Groß of Google Project Zero
CVE-2019-8523: Apple
CVE-2019-8524: G. Geshev working with Trend Micro Zero Day Initiative
CVE-2019-8558: Samuel Groß of Google Project Zero
CVE-2019-8559: Apple
CVE-2019-8563: Apple
CVE-2019-8638: found by OSS-Fuzz
Webdriver Mac
CVE-2019-8639: found by OSS-Fuzz
Entry updated May 30, 2019
WebKit
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, and Mojave 10.14.4
Impact: Processing maliciously crafted web content may lead to arbitrary code execution
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2019-8536: Apple
CVE-2019-8544: an anonymous researcher
WebKit
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, and Mojave 10.14.4
Safari 12 Webdriver Download Mac Download
Impact: Processing maliciously crafted web content may disclose sensitive user information
Description: A cross-origin issue existed with the fetch API. This was addressed with improved input validation.
CVE-2019-8515: James Lee (@Windowsrcer)
WebKit
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, and Mojave 10.14.4
Impact: Processing maliciously crafted web content may lead to arbitrary code execution
Description: A use after free issue was addressed with improved memory management.
CVE-2019-7285: dwfault working at ADLab of Venustech
CVE-2019-8556: Apple
WebKit
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, and Mojave 10.14.4
Impact: A malicious website may be able to execute scripts in the context of another website
Description: A logic issue was addressed with improved validation.
CVE-2019-8503: Linus Särud of Detectify
WebKit
Safari 12 Webdriver Download Mac Installer
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, and Mojave 10.14.4
Impact: Processing maliciously crafted web content may result in the disclosure of process memory
Description: A validation issue was addressed with improved logic.
CVE-2019-7292: Zhunki and Zhiyi Zhang of 360 ESG Codesafe Team
WebKit
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, and Mojave 10.14.4
Impact: A sandboxed process may be able to circumvent sandbox restrictions
Description: A memory corruption issue was addressed with improved validation.
CVE-2019-8562: Wen Xu of SSLab at Georgia Tech and Hanqing Zhao of Chaitin Security Research Lab
WebKit
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, and Mojave 10.14.4
Impact: Processing maliciously crafted web content may lead to universal cross site scripting
Chrome Webdriver Download
Description: A logic issue was addressed with improved validation.
CVE-2019-8551: Ryan Pickren (ryanpickren.com)
Additional recognition
Safari
We would like to acknowledge Ryan Pickren (ryanpickren.com), Nikhil Mittal (@c0d3G33k) of Payatu Labs (payatu.com) for their assistance.
Entry updated May 30, 2019
WebKit
We would like to acknowledge Andrey Kovalev of Yandex Security Team for their assistance.